Cybersecurity Careers

Interested in a career in cybersecurity? With high demand and an insufficient amount of qualified cybersecurity professionals, now is a great time to enter the industry. In this post, we’ve collected some standard job titles, their typical requirements, and the average salaries to expect.
Interested in cybersecurity career paths? With the current market combining high demand with an insufficient amount of qualified cybersecurity professionals, now is a great time to enter the industry.
In this post, we’ve collected some standard job titles, their typical requirements, and the average salaries to expect.
What is Cybersecurity?
Cybersecurity, also called information technology security, is the protection of computer systems and networks from information disclosure, theft of, or damage to their hardware, software, or electronic data, as well as from the disruption or misdirection of the services they provide.
In more simple terms, it is the practice of protecting sensitive digital information from unauthorized access.
Why pursue a career in Cybersecurity?
Frankly, demand is booming for cybersecurity professionals. According to research by Cybersecurity Ventures, “the number of unfilled cybersecurity jobs grew by 350 percent, from 1 million positions in 2013 to 3.5 million in 2021 … and an estimated 1.8 million cybersecurity jobs will go unfilled.” (1)
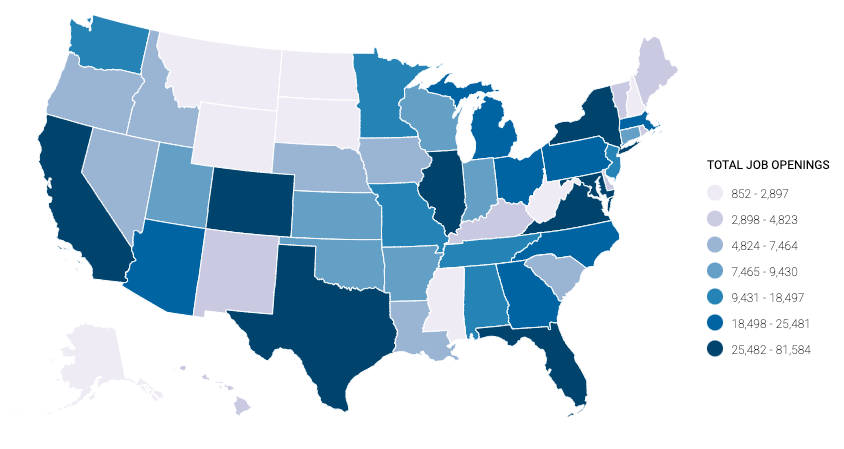
For those looking to switch jobs or careers entirely in Cybersecurity, there are myriad opportunities. According to Cyber Seek, there are over 775k jobs available in the US alone, especially in tech hotspots of the country like California, Texas, Florida, Virginia, and New York. (2)
Recent years have seen digital transformations in the form of new platforms (i.e., the cloud), technologies, and software. Paired with recent waves of new regulations on the digital space due to growing privacy concerns and recent high-profile breaches, the cybersecurity industry is struggling to keep up and is faced with a growing skill shortage.
For many organizations, current staff training levels leave companies unprepared for new digital risks and compliance requirements, and bad actors are taking advantage.
Related article: Top 3 Cybersecurity Pain Points
Rise In Cyber Attacks
Despite the persistent cultural mental image of hackers as a single individual in a dimly lit basement, in the digital age cyberhacking has become a lucrative, multi-billion dollar industry. (3) And, with the rise of advanced technology such as artificial intelligence, machine learning, and automation, the industry has seen an exponential increase in the number, frequency, and complexity of cyber attacks.
This is exacerbated by the COVID-19 pandemic that forced a rushed adoption of remote working and left companies to fumble through the transfer to cloud hosting platforms and employees working from home with lower security levels and far more access points.
The cyber skill gap highlights vulnerabilities concerning newer technologies and platforms that, if left open to attackers, could cripple a company before it’s aware of the risk.
Organizations, both big-name and boutique, are rapidly hiring cybersecurity professionals to fill skill gaps on their teams, particularly those concerning newer technologies and platforms. For those interested in Cybersecurity, there is no better time to enter the field.
Entry-Level Roles
Information Security Analyst
Average salary: $101,764*
Information Security Analysts are the gatekeepers and security guards of information systems. These professionals plan and execute security measures to shield an organization’s computer systems and networks from infiltration and cyberattacks.
Security Specialist
Average salary: $89,533*
A Security Specialist is responsible for maintaining the security of an organization’s database, ensuring that it’s free from cyber threats and unusual activities.
They upgrade hardware and software applications, configure networks to improve optimization, address unauthorized database access, troubleshoot system discrepancies, conduct security audits on the system, and improve automated processes.
Digital Forensic Investigator
Average salary: $85,015*
A Digital Forensics Investigator uses digital evidence to solve virtual crimes. Should a security breach occur, resulting in stolen data, a Digital Forensic Investigator will attempt to recover data. This can include documents, photos, and emails from computer hard drives and other data storage devices that have been deleted or damaged.
IT Auditor
Average salary: $95,203*
Information Technology (IT) Auditors protect internal controls and data within an organization’s technology system. They safeguard sensitive information by identifying network weaknesses and creating strategies to prevent security breaches.
Mid-Level Roles
Security Systems Administrator
Average salary: $99,132*
A Security Systems Administrator is someone who gives expert advice to companies regarding their internal security procedures and helps detect network weaknesses that may make them vulnerable to cyber-attacks.
Security Systems Administrators are in charge of the daily operation of security systems and can handle things like systems monitoring and running regular backups, setting up, deleting, and maintaining individual user accounts, and developing organizational security procedures.
Penetration Tester
Average salary: $118,287*
Penetration Testers, often abbreviated as “pen testers”, perform simulated cyberattacks on a company’s computer systems and networks. These authorized tests identify security vulnerabilities and weaknesses before malicious hackers have the chance to exploit them.
Security Engineer
Average salary: $113,903*
Security Engineers are responsible for testing and screening security software and monitoring networks and systems for security breaches or intrusions.
Security Architect
Average salary: $152,308*
Security Architects assess an organization’s IT and computer systems to identify strengths and weaknesses. They also conduct penetration tests, risk analyses, ethical hacks, and assess routers, firewalls, and systems to determine efficacy and efficiency.
Cryptographer
Average salary: $154,545*
Cryptographers secure computer and information technology systems by creating algorithms and ciphers to encrypt data. They often also carry out the duties of a cryptanalyst, deciphering algorithms and ciphering text to decrypt information. Cryptographers also analyze existing encryption systems to identify weaknesses and vulnerabilities.
Cybersecurity Manager
Average salary: $120,130*
Cybersecurity Managers monitor the channels through which information flows into and out of an organization’s information network. They are responsible for observing all of the operations occurring across the network and managing the infrastructure that facilitates those operations.
Senior Level Roles
Senior Manager of IT & Security Compliance
Average salary: $161,080*
A Senior Compliance Officer manages an organization’s compliance team to ensure adherence to industry guidelines. They check for, investigate, and resolve any unethical or illegal behavior, identify regulatory compliance issues, and conduct compliance risk assessments.
Director of IT Security
Average salary: $165,416*
An Information Security Director oversees the information technology security operations of a business. Responsibilities often include security assessments, department budget management, training employees, managing security programs, and crisis management.
Cybersecurity Architect
Average salary: $125,145*
A Cybersecurity Architect plans, designs, tests, implements, and maintains an organization’s computer and network security infrastructure.
Chief Information Security Officer (CISO)
Average salary: $194,648*
A Chief Information Security Officer (CISO) is the executive within an organization responsible for establishing and maintaining the enterprise’s vision, strategy, and program to ensure information assets and technologies are adequately protected. The CISO directs staff in developing processes, responds to incidents, establishes standards and controls, manages security technologies, and directs the establishment and implementation of policies and procedures.
Bug Bounty Specialist
Average salary: $138,009*
Also known as an “Ethical” or “White Hat Hacker”, a Bug Bounty Specialist is an individual that takes advantage of deals offered by websites, organizations, and software developers by which individuals can receive recognition and compensation for reporting bugs, especially those regarding security exploits and vulnerabilities.
Breaking Into The Field
The market in 2023 is red-hot, to say the least. With frequent cohorts of cybersecurity graduates training in the latest technologies and platforms and high amounts of turnover as skilled workers trade up for more convenient and lucrative jobs, the talent pool is both deep and competitive.
To be a competitive applicant for these cybersecurity career paths, gaining an educational certificate from an established training organization like Flatiron School can supercharge your career and make you stand out among a sea of hopefuls.
Ready to take the next step? Start with our Free Cybersecurity Prep Work, or check out the Cybersecurity Course Syllabus that will set you up for success with the skills to launch you into a fulfilling and lucrative career.
Related Articles:
What Certifications Do You Need for Cybersecurity?
How to Get into Cybersecurity: 6 Questions from Beginners
Top 3 Cybersecurity Pain Points in 2022
* Salaries cited current as of April 2023, ZipRecruiter
Sources:
- https://www.linkedin.com/pulse/future-cybersecurity-job-market-2022-amit-doshi/
- https://www.cyberseek.org/heatmap.html
- “Cybersecurity: Hacking has become a $300 billion industry,” InsureTrust
- https://www.isc2.org/News-and-Events/Press-Room/Posts/2021/10/26/ISC2-Cybersecurity-Workforce-Study-Sheds-New-Light-on-Global-Talent-Demand
Disclaimer: The information in this blog is current as of June 30, 2022. Current policies, offerings, procedures, and programs may differ.



