The Flatiron School Advantage
Upcoming Course Start Dates
Upcoming Course Start Dates
What is Cybersecurity?
Possible Career Paths
The demand for Cybersecurity professionals is growing rapidly. In fact, The Bureau of Labor & Statistics indicate a 35% national growth for Security Analysts, which is much faster than the average of all occupations. Here are some in-demand jobs you could land:
Cyber Engineer
Average Salary: $116,497*Cyber Engineers, sometimes called Information Security Engineers, identify threats and vulnerabilities, then apply their skills to developing and implementing high-tech solutions to defend against hacking, malware and ransomware, insider threats and all types of cybercrime.
*ZipRecruiter (September 2023)
Security Analyst
Average Salary: $111,141*Security Analysts are responsible for ensuring that the company’s digital assets are protected from unauthorized access. This includes securing both online and on-premise infrastructures, weeding through data to filter out suspicious activity, and mitigating risks.
*ZipRecruiter (September 2023)
Penetration Tester
Average Salary: $118,358*Penetration Testers help organizations identify and resolve security vulnerabilities affecting their digital assets and computer networks. They try to break things by simulating a cyber attack and attempting to breach networks and information systems.
*ZipRecruiter (September 2023)
Security Consultant
Average Salary: $116,514*A Security Consultant works as a supervisor for all security measures necessary to effectively protect a company or client’s assets. Security Consultants use their expertise to assess possible security threats and create contingency protocols and plans for when violations occur.
*ZipRecruiter (September 2023)
Over $8.6 Million Awarded in Scholarships
We believe that anybody who wants to pursue a career in tech should be able to do so – regardless of how they identify, their background, or financial circumstances.
We offer three different scholarships – Access Scholarship, Merit Scholarship, and Women Take Tech – to support our students in their pursuit of a better life through education.
Learn MoreStudent Success Stories
Not sure if our course is right for you? Hear from students who’ve been where you are. These students took charge of their futures, enrolled in our Cybersecurity course, and jumped head-first into an exciting career.
Great companies have hired Flatiron School graduates
Upcoming Course Start Dates
| Start Date | Pace | Location | Discipline | Status |
|---|---|---|---|---|
|
May 6, 2024
May 6, 2024
|
Part-Time | Online | Cybersecurity | Few Spots Left! |
|
June 3, 2024
Jun 3, 2024
|
Part-Time | Online | Cybersecurity | Open |
|
June 17, 2024
Jun 17, 2024
|
Part-Time | Online | Cybersecurity | Open |
|
June 24, 2024
Jun 24, 2024
|
Full-Time | Online | Cybersecurity | Open |
Become a Cybersecurity Engineer in as little as 15 weeks
Your Life Won’t Wait For A Career Change
Our students understand that there’s a lot of hard work ahead of them, but we also understand the need for flexibility. We deliver a structured learning experience that adjusts to your lifestyle. Your admissions representative will help you choose the option that makes sense for you.
Full-Time
You’re ready to commit to a full-time course load. You’ll graduate in 15 weeks thanks to a rigorous schedule: 8 hours a day, Monday to Friday.
- 15 weeks long
- In-person or online
- Synchronous learning with your cohort
- Course highlights:
- Group work with instructor help
- Paired with design sessions
- Lab time with instructional staff
Part-Time
Our part-time course is designed for busy people. If you don’t have 8 free hours to dedicate a day (same), then our part-time course is for you.
- Paced to complete at 40 weeks
- Online only
- Asynchronous learning at your own pace
- Course highlights:
- Pre-recorded lessons
- Optional live lectures and office hours
- Discord with classmates and instructors
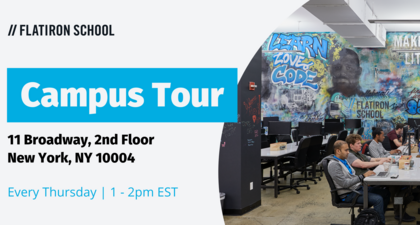
Attend An Event
Whether you attend online or on-campus, a Flatiron School event is a great way to get insight into student life, community, and our curriculum.
Cybersecurity Curricululm
Our curriculum incorporates the latest emerging technologies, including artificial intelligence (AI) tools. During class, we have a hands-on, community approach to learning, one that includes lab work, creating a real-world portfolio, and 1-on-1 instructor access.
Download The SyllabusNo matter where you’re starting from, Prework is meant to build your foundational knowledge and prepare you for success in the course. Learn to leverage artificial intelligence, machine learning, and ChatGPT to assist with various concepts and tasks.
Everyone starts out learning the fundamentals of Cybersecurity. You’ll learn about network security components, such as Ethernet and Wi-Fi, and explore systems security with concepts such as operating systems architecture and system exploits. Learn to leverage artificial intelligence, machine learning, and ChatGPT to assist with various concepts and tasks.
Next, you’ll be briefed on military principles of intelligence analysis and the concept of cyber warfare. You’ll cover a range of topics on securing the modern enterprise from outside threats including governance, risk management, and compliance. Learn to leverage artificial intelligence, machine learning, and ChatGPT to assist with various concepts and tasks.
Python and engineering solutions are up next. You’ll use basic coding and analysis to create Python scripts and automation and learn to analyze logs in various network devices. Learn to leverage artificial intelligence, machine learning, and ChatGPT to assist with various concepts and tasks.
After developing coding skills, you’ll use your new knowledge to perform penetration testing for vulnerabilities in applications and network security resources. Learn to leverage artificial intelligence, machine learning, and ChatGPT to assist with various concepts and tasks.
Next, you’ll learn the components of cryptography with hands-on experience configuring a web server with SSL/TLS, interfacing with Certificate Authorities, issuing certificates, and securely configuring SSH. Learn to leverage artificial intelligence, machine learning, and ChatGPT to assist with various concepts and tasks.
The course finishes out with a scenario capstone activity. You’ll use everything you’ve learned to work through the particulars along multiple paths and prepare to highlight it in your professional portfolio. Learn to leverage artificial intelligence, machine learning, and ChatGPT to assist with various concepts and tasks.
Now Offering Cybersecurity Prep Work

Tuition
Whether you are full-time or part-time, our Cybersecurity program is the same price.
- $16,900
- $99 deposit
We have 3 easy ways to pay:
- Pay up front & in full
- Pay with a traditional loan (as low as $388/month)
- Pay with a payment plan (as low as $683/month)
Frequently Asked Questions
While they may vary with each course and each school, online cybersecurity engineering bootcamps are short-term and often rigorous training programs to help students learn the skills they need to become professional cybersecurity engineers.
We get asked this a lot — and it’s a great question — and encourage you to think about what you mean by “worth it.” If “worth it,” to you, means attending a cybersecurity engineering bootcamp, learning the skills you need to become a cybersecurity engineer, and landing a job as one, then yes, good cyber engineering bootcamps are certainly worth it.
In fact, that’s what most bootcamps set out to help you do — and the best ones will indeed help you get there.
But if you’re simply looking to brush up on your cybersecurity knowledge without a goal to work in cyber, then a full-time or part-time bootcamp would not end up being worth it for you.
If you’re looking to join the cybersecurity field professionally, though, it’s a growing and lucrative field — and the best bootcamps can help you break into it.
Read more about whether or not cybersecurity bootcamps are worth it for you and your goals.
Employers value people who can do the job and who can learn and adapt quickly on the job. By successfully completing a bootcamp, you’re demonstrating that you can “do” as evidenced by your projects, and that you can “learn” as evidenced by completing the program.
At Flatiron School, you’ll be able to demonstrate both. You’ll learn how to learn because new technologies and tools appear on the market everyday. Our approach enables graduates to learn and apply new tools when needed. In other words, it’s not just the skills themselves that are important to hiring managers, but how you go about acquiring skills to complete a job that sets you apart.
In many ways, cybersecurity bootcamps definitely do work, and there’s a lot of proof behind that statement.
But it’s better to first ask yourself, “What do I want to get out of attending a cybersecurity bootcamp?” Asking yourself what your goals and ambitions are is how you’ll know if a bootcamp would work for you.
Some people want to just become acquainted with the cybersecurity field, which is great, but a full-time bootcamp might not be the best route if you’re looking for a basic understanding of cybersecurity.
If your goal is to learn to become a cybersecurity engineer, then yes, cybersecurity bootcamps do work.
We don’t require you to have prior experience to apply for the Cybersecurity Engineering program. Our admissions requirements are being at least 18 years old, having a high school diploma, a GED or equivalent credential, having a native or highly proficient fluency in English, and completing the admissions process.
Before joining your cohort on Day 1, you will have to complete around 40 hours of coursework called Prep to learn the basics of cybersecurity so you are prepared to get started straight away.
The Live program is 15 weeks, but rather than going to a campus, you’ll be logged on learning remotely full-time. Both on-campus and Live programs monitor attendance daily. The Flex program gives students up to 60 weeks to complete the curriculum, and offers the most flexibility day to day. Students enrolled in Flex programs must attend 10 check-ins in order to be eligible for graduation but are not otherwise required to attend live instructional activities.
The price of our courses reflect our unique approach to learning and support. There are many free resources that can help you learn any discipline, but given the complexity of the topic they can be difficult to navigate independently. Furthermore, students often rave about the camaraderie they establish with instructors, other students, coaches, and alumni – all valuable networking opportunities when it comes to a job search. Our courses and support after graduation are built specifically to provide the structure and community that’s required to be successful.
As for our more traditional competitors – those who are priced similarly and offer live instruction – most haven’t been around as long as Flatiron School, so they may not have the same depth of expertise, employer partner relationships, or alumni network.
The first step is to fill out a written application. Once submitted, you will receive prompts from the admissions team to schedule an interview and take a 15 min aptitude assessment. During the interview a member of the admissions team will learn about your learning needs, career goals, and help you decide whether the program is the right fit for you. If you passed your assessment, we will give you the admissions decision after your interview.
You have a few options in terms of financing your enrollment in one of Flatiron School’s courses. See all of your options on our Tuition & Financing page.
We also offer initiatives that can help to offset the cost of tuition on our Scholarships and Diversity Initiatives page.
The Flatiron School Career Services team exists to help get you hired. You’ll receive guidance on how to:
- Build and Optimize your LinkedIn Profile and Resume
- Ace your behavioral and technical interviews
- Grow your network of tech professionals
- Connect with Flatiron School employer partners
- Negotiate your salary
- Optimize your job search using AI
- Track job search activity using Huntr
You’ll partner with a dedicated Career Coach regularly to make forward progress each week, with up to six months of one-on-one support after graduation.
Our graduates have and continue to make lasting impact in a range of companies from small startups to Fortune 500 companies.
Companies who have hired our grads include:
- Apple
- Microsoft
- IBM
- Shopify
- VOX
- BuzzFeed
- Spotify
- Accenture
- Intel
- Kickstarter
- The New York Times
- Thought Works
- Goldman Sachs
- PWC
- Citi Bank
- Dow Jones
- Akamai
You can view our latest job placement rates in our Jobs Report.
We’ve issued a third-party examined Jobs Report each year since 2014 and remain committed to honesty and transparency with student outcomes.
If you would like to connect with a member of our team, please simply schedule a chat with one of our Admissions representatives.